






Protecting Information Is a Strategic Challenge.
With OBAKE, organizations gain a new ally to face this challenge with stronger protection and greater trust.





Who is OBAKE for?
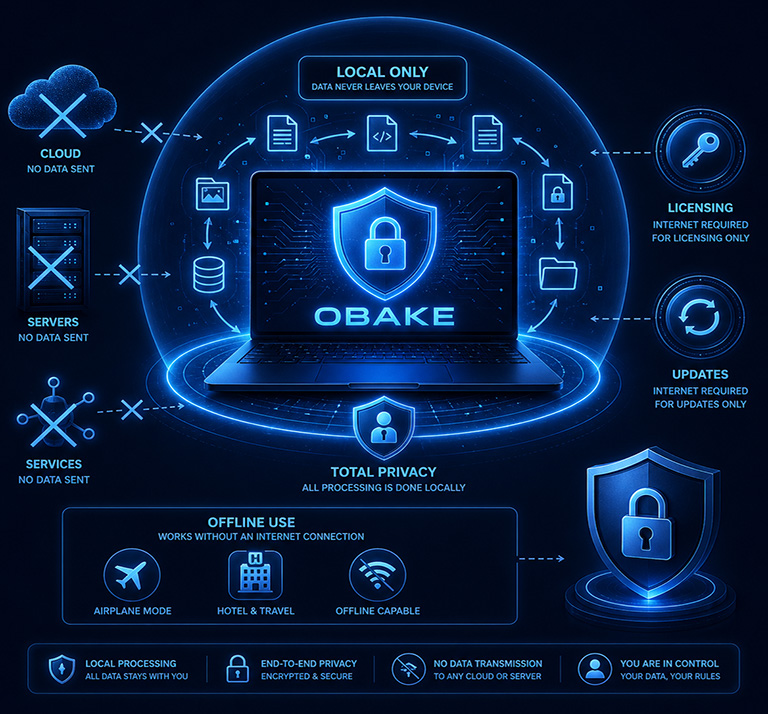
End-to-end encryption and intelligent controls to protect sensitive information at every stage:
storage, transit, sharing, and backup.









Built with a highly efficient architecture to deliver security, speed, and exceptional ease of use for information sharing.
Start a POC or Contact our Team
Tell us about your use case, questions, or evaluation needs.
